Member-only story
How to be an Amateur Bot Hunter
Social networks are full of fake accounts, tracing their networks and observing their behavior can reveal interesting things about how the world works. But only if you can find them!
I have a long running fascination with scammers. From the very first moment my father introduced me to the film The Sting, nothing has proved more entertaining than exploring an elaborately constructed con. It’s a form of storytelling in a way. The best scams say more about how their victims see themselves than the attackers.
When fake accounts started to take over social media (and they have taken over social media) I found the perfect hobby. These networks are used in scams, but they are also commodities. Accounts are bought, sold, rented — used for one purpose, but generating passive income from other activities. You can see evidence of this in the demographics of the bots’ fake identities. Accounts change names, topics, profile pics, pretending to be completely different races, genders, sometimes even changing from adults to children.
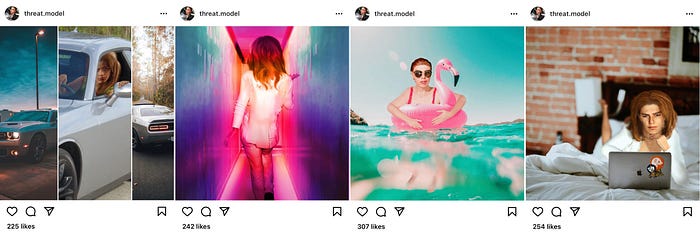
Recently, I’ve been spending my time researching a massive network running ambassador scams on Instagram, but in writing that post I found myself unable to stop from digressing into the mechanics of the amateur bot hunting itself — writing long paragraphs and then cutting them out over and over again.
So this is intended as a companion piece to that article. A tutorial on how I found the Vincere network and collected the data to explore it.
Pick Your Platform
One of the hardest parts of bot hunting is attribution. Good attribution relies on information most social networks will not expose to you in order to protect users privacy. So while actors absolutely operate across platforms, network analysis tends to stay on a single one.
Some platforms are easier than others. Twitter has no problem listing an account’s followers and who they are following. Activity data is just an API request away. Facebook, on the other hand, will restrict this data according the permissions your account has.
In general, anything that’s visible to you as a logged in user is usually accessible via an official API. As long as you respect the rate limits, you can usually grab the data you need…